|
|
LDAP IntegrationTable of contents
Account information can be integrated with an external LDAP database to allow accounts defined within the SIS to provide authentication for e-mail, wi-fi, or other LDAP-aware services. This documentation describes the LDAP intergration support provided within the SIS. Integration with LDAP is not required for operation of the SIS. Some account management functions (e.g. deleting an account) can only be performed on the LDAP Account form, but this shouldn't be taken to imply that LDAP is required or in use. LDAP Configuration
The Server URL should be formatted as required by the installed version of LDAP. It may be just a host name, or include a protocol specification such as ldap, ldaps, or ldapi. Base DN is the origin in the database where all information managed by the SIS will be created. The LDAP database must already contain this definition; it will not be created automatically. Group DN defines the origin for group data, which is managed using the posixGroup objectClass, with individual group members listed by memberUid. Auth CN must specify a distincguished name (dn) with full access to the database for inserting, updating, or deleting records. Auth Password is the password for the Auth CN specified. Often this will be the rootdn for the LDAP server, but can be any dn with sufficient privileges. This dn must be configured with the LDAP server with "size=unlimited" for queries, or some management tasks may not function! AccountsEach person defined in the database can have one or more accounts associated with them. Each account has a unique login name, and may be used for access to it's own combination of services.
ServicesSupport for specific applications is organized around Services. The service definition includes an LDAP objectClass to define what type of information should be included in the associated LDAP record, but In addtion to the service code and description for an LDAP Service, these records include:
|
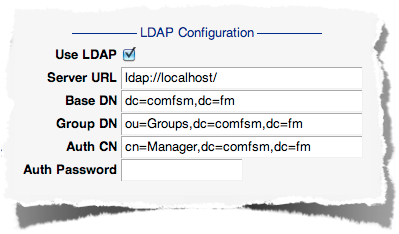 Information for use of an LDAP server is configured on the
Information for use of an LDAP server is configured on the 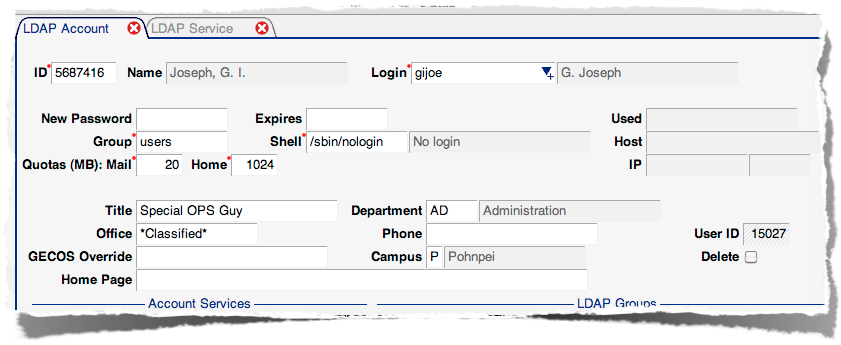 Along with a login and password, account information includes UNIX-specific data like group and shell, as well as general information like title, office location, phone number, and campus. This information is used in different ways by the services that are associated with an account. Details of how services use each field are described next.
Along with a login and password, account information includes UNIX-specific data like group and shell, as well as general information like title, office location, phone number, and campus. This information is used in different ways by the services that are associated with an account. Details of how services use each field are described next.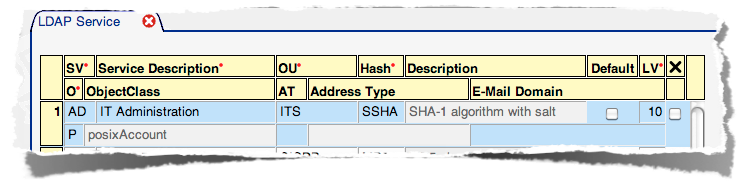 also defines other characteristics such as what type of password should be used (called a
also defines other characteristics such as what type of password should be used (called a